Sponsored by Gigamon
Sponsored by CyberArk
Fortune 100 Company Accelerates Operational Agility with CyberArk Blue Prism Integration
Sponsored by Cyberark
The CISO View - Protecting Privileged Access in Robotic Process Automation
Sponsored by Cyberark
The New CISO Mandate: Securing All Application Secrets
Sponsored by Gigamon
2022 Survey Results | Ransomware, Cryptojacking and Beyond: Emerging Security Trends
Sponsored by Proofpoint
2022 Voice of the CISO
Sponsored by RSAC 2022
RSAC 2022 | Call For Speakers Submission Trends
Sponsored by Hexagon
ICS Cybersecurity: Protecting the Industrial Endpoints That Matter Most
Sponsored by Hexagon
SANS Institute - Industrial Control System Resilience
Sponsored by Splunk
5 Key Ways CISOs Can Accelerate the Business
Sponsored by Proofpoint
Threat Report: 2022 State of the Phish
Sponsored by Proofpoint
Building a Sustainable Security Culture - and Why it Matters
Sponsored by Proofpoint
Measuring Security Awareness Impact for Long Term Success
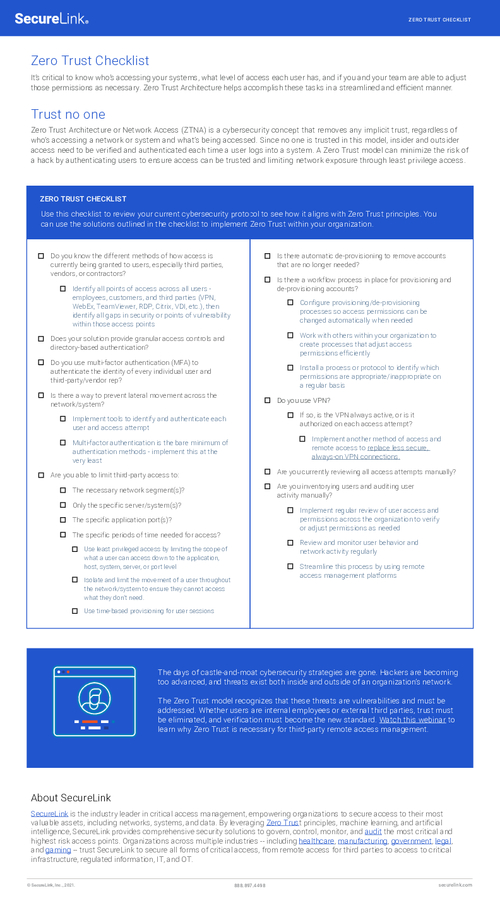
Sponsored by SecureLink