Sponsored by Splunk
Sponsored by Splunk
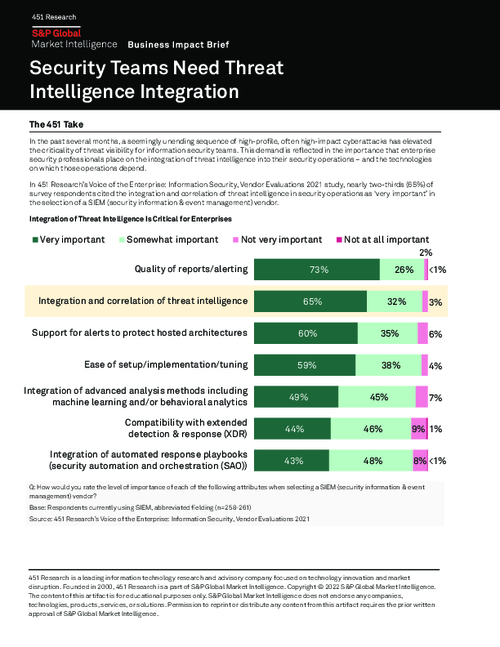
451 Research: Security Teams Need Threat Intelligence Integration
Sponsored by Dell Technologies
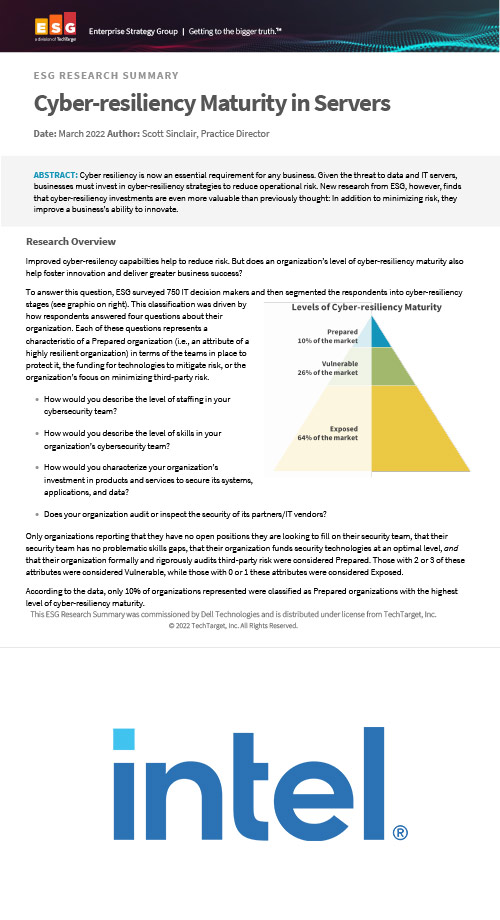
Cyber-resiliency Maturity in Servers
Sponsored by Dell Technologies
Cyber-resiliency Maturity in Data Storage
Sponsored by Dell Technologies
Integrated Cyber Security Defense Strategy
Sponsored by Dell Technologies
The Ransomware Survival Guide
Sponsored by Dell Technologies
All-in-one VMware Multicloud Data Protection
Sponsored by Dell Technologies
Dell Trusted infrastructure - Secure your Organization for the Modern Era
Sponsored by Palo Alto
2022 Attack Surface Threat Report
Sponsored by Palo Alto
Modernize Your SOC with This Playbook
Sponsored by Palo Alto
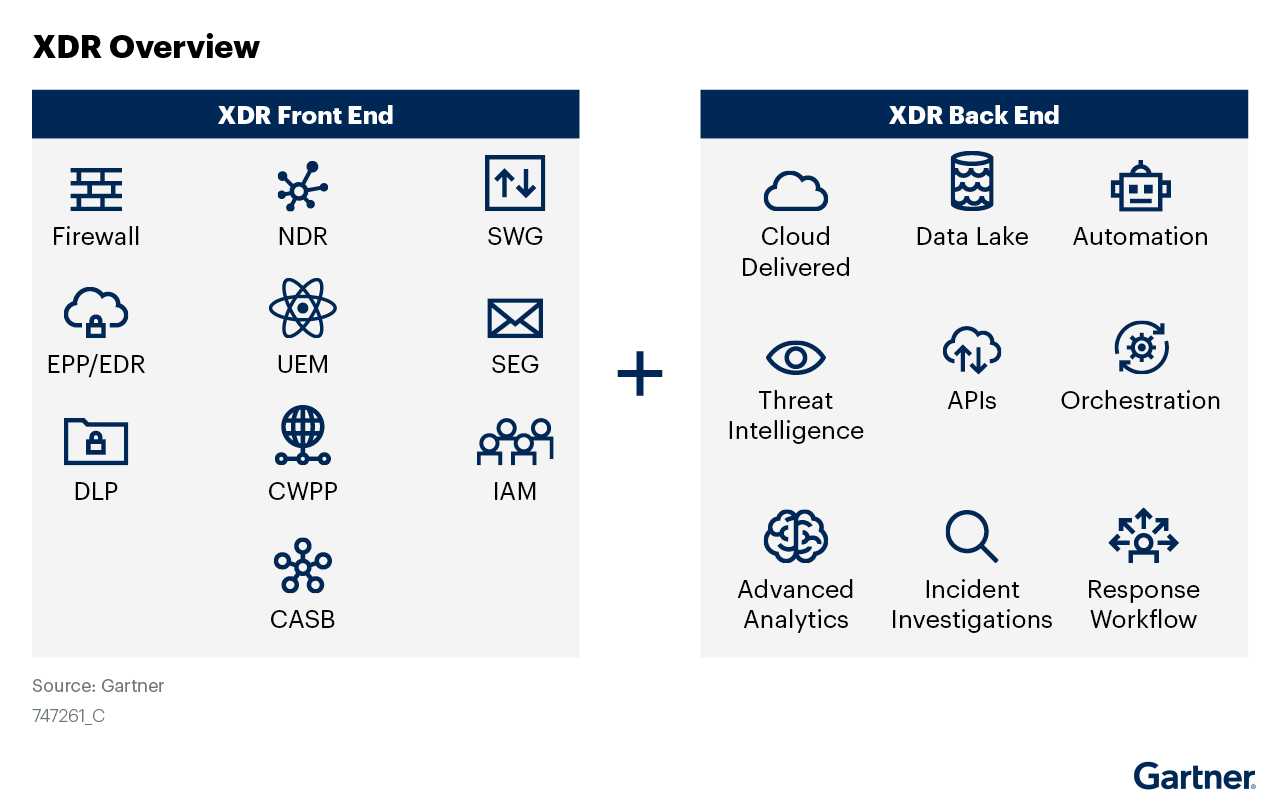
Gartner Market Guide for Extended Detection and Response
Sponsored by Palo Alto
BLOCKED! Five Strategies for Ironclad Endpoint Security
Sponsored by CrowdStrike
Forrester Study : The Total Economic Impact of Humio, A CrowdStrike Company
Sponsored by CrowdStrike
Humio Scalability Benchmark Report
Sponsored by Token Ring