Sponsored by Dragos
Sponsored by Cyberark
Securing Identities Across the Software Supply Chain and Development Environments
Sponsored by Splunk
Bridging the Data Divide
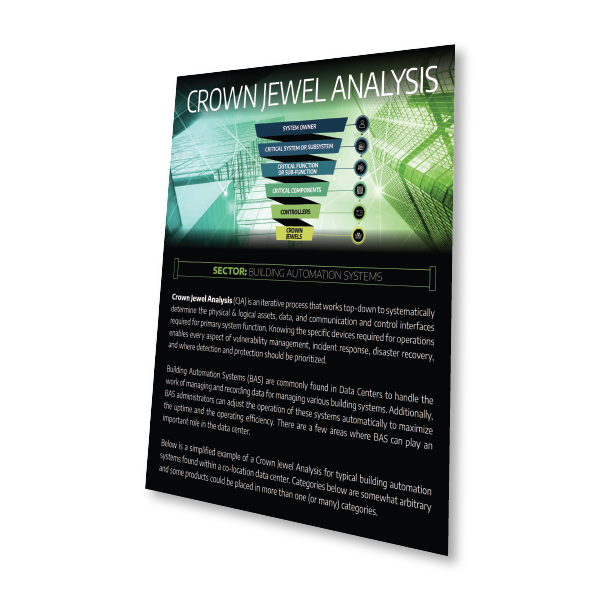
Sponsored by ForeScout
Reducing Risks from IoT Devices in an Increasingly Connected World
Sponsored by ForeScout
Total Visibility: The Master Key to Zero Trust
Sponsored by ForeScout
Going Selectively Active for Comprehensive OT Visibility
Sponsored by ForeScout
SANS Review | Device Visibility and Control: Streamlining IT and OT Security
Sponsored by One Identity
The Top Five Ways to Relieve the Pain of Managing Hybrid AD Environments
Sponsored by iovation
Account Takeover: Responding to The New Wave
Sponsored by SparkPost
Email's Need For The Security Advantages of Cloud Infrastructure
Sponsored by Certified Security Solutions (CSS)
Providing Strongly Authenticated Device Identity During the Era of IoT
Sponsored by Venafi
Are You Vulnerable to an SSH Compromise?
Sponsored by FireEye
Good Endpoint Security Is Key to Business Success
Sponsored by Cisco
Have You Plugged the Security Gaps
- «
- 1 (current)
- 2
- 3
- »